Obsolescence is a serious risk. Would you fly in an aircraft that was three years past its maintenance cycle? The same principle applies to computer hardware. Aging hardware and software not only puts a single system at risk, but could also put everyone else on your network at risk too.
Old hardware can create vulnerabilities that online criminals can take advantage of to breach systems. Not only do you have to worry about individuals creating windows of opportunity, but now there’s the chance that by simply using your software or equipment—because it’s outdated—could be creating weak spots for hackers to exploit in your network security.
The longer a piece of software or hardware has been available to the public, the longer digital criminals have had to find their weaknesses, and the less likely you’ll be able to protect yourself against their intrusions.
Most major software vendors publish their support life cycle and end-of-life policies, so customers are aware of the date at which the product will cease to receive periodic updates such as security patches, or support is gradually phased out. This makes it easier to plan and manage a technology refresh well in advance.
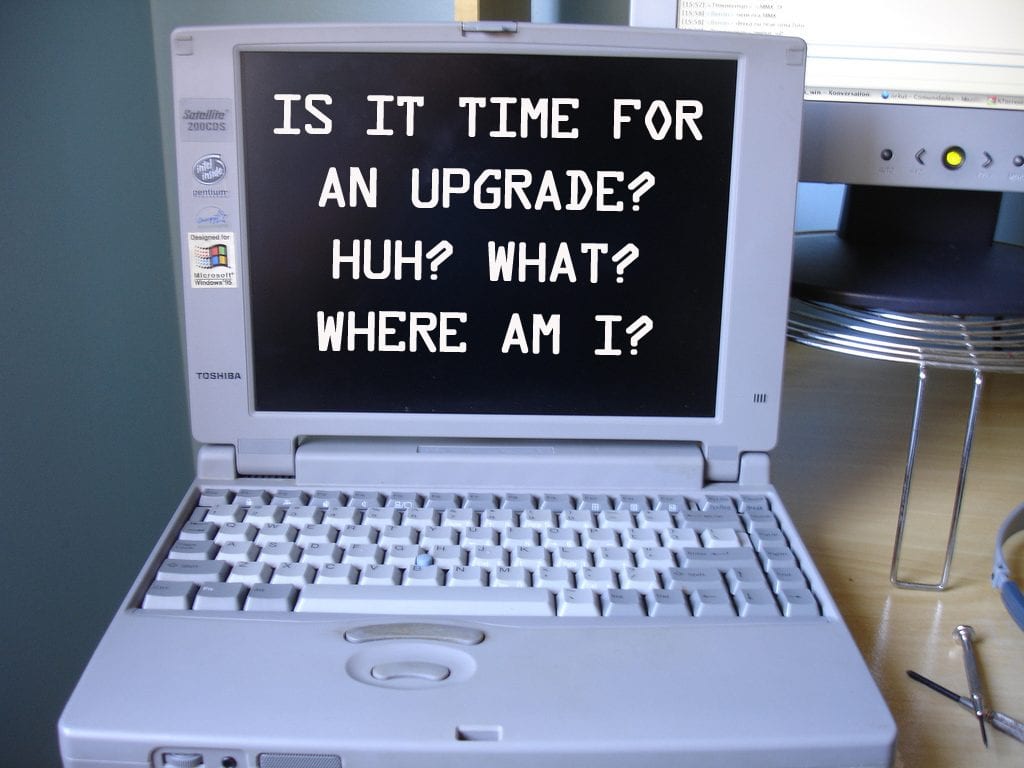
Just because it works, doesn’t mean it’s at its best. You may feel it’s hard to justify splashing out on new hardware, but older laptops and desktops don’t work with many new security updates, and don’t support measures such as comprehensive encryption or advanced authentication. Not to mention that hardware over three years old costs significantly more to maintain and can hinder your productivity.
A common reason for resisting migration to the most recent and secure technology is, of course, cost. But failure to do so in an age of increasing digital information vulnerability is a false economy.
Policies protect you, and not only at your job. Weinberg College IT understands the ever evolving technology landscape, and along with it, the risks of security threats that result from outdated hardware and software. Therefore, our hardware and software support policies are designed to ensure that Northwestern University’s data, network, and end-user privacy remain compliant, and the risk of a breach remain low.
Do you have an old computer sitting on your desk at home? How confident are you that everything is secure on it? The same approach that IT departments have should be taken and applied at home when it comes to computer obsolescence. Yes, your children may use the computer only for gaming or word processing, but did you know that those games are still open to the world, and lurkers are plentiful, looking for potential vulnerabilities. So, always make sure your systems are up to date with security patches, that you have a backup plan in place. And, if it’s too old, replace it.
Very interesting information! I’m a beginner to network security and currently doing part-time ccna course from 1training. (Here’s the course link: https://www.1training.org/course/complete-cisco-networking-course-bundle/)
Please advise if Weinberg College offers an associate degree in network security that covers the topics offered in most cisco courses? Thank you in advance.
Hi Sarah,
Weinberg College does not offer an associate degree in Network Security. However, Northwestern University does offer a Cybersecurity Bootcamp. For more information go to https://bootcamp.northwestern.edu/cybersecurity/
Best,
Alex
If your computer is 5 or more years old, then there must be a high risk for being attacked by the malware, so I will suggest you regularly update the system as well as the antivirus that is installed on your system to prevent further infection.
Here I get to know some useful ideas about computer technology. This type of technology is just really very helpful to me. Thanks for sharing such useful information. Keep sharing.
Hi! I am John, managing director of bugsbd.com. I have read this content fully. A lot of contents full of bullshit waste our time. But I’m really surprised after reading your content. I must say, It is much unique and informative. I have no questions anymore about this. Actually, this content can be very helpful for all of us. Anyone can read this type of content and can get benefited. By this content the author trying to understand the merit and demerit. It is quite readable and easily understandable. This type of content can develop our knowledge. So we should follow this type of content. I am really interested to this after reading it. You should continue your content writing.
Yes, I agree this content is amazing and well constructed with good advices and unique and helpful and also useful information. I will plan to upgrade my 10 year old computer even though it runs linux os really fast and well. The software is always up to date but I guess the cpu itself could be vulnerable to attack if anyone knew how to do it so I will upgrade the system and use this one for home video security where it will be useful. But I have not had problems and use a double firewall so nobody can get through because I also monitor for cyber attacks and if they hacked me I would snapshot all their information and they would be in big trouble. My good advice is to run linux as it is much more secure than windows and mac and if there are any security issues exposed it gets a fix issued right away where windows or mac take weeks or months.
Weinberg College IT understands the ever evolving technology landscape
Thanks, Alex…
I completely agree with the fact that old computers are vulnerable to cybersecurity threats.
So, such computers should be replaced with modern computers with better security features.
Cybersecurity threat has emerged as one of the major issues with the use of the internet.
Everyone should be aware of the precautionary measures to prevent any kind of data loss.
To learn more, visit https://www.geektek.com/cyber-security-risks-solutions-and-services/
Thanks for your good website and information !
I have travelling problems as per my profession because I am a nursing student and I need to have it at any cose but I have chosen best Laptops For Nursing Students for my work and it is just amazing.
Your work looks very fine, and I recommend that you take the aid of Software Development USA to build software that will help you with your design work.
With the continuously evolving technology, the online development frameworks became far more sophisticated and organised, delivering superlative websites built as per the business requirements is one among these. IOT hardware devices
Thanks for your good website and information !
Best,
Kristoffer Elsa
If the computer is old, what security risk does it present if:
– you the the drive with new SSD
– you upgrade memory
– you reimaged with Windows 10, including latest updates
– you install Defender, including latest updates
– you install Bitlocker, including latest updates
The premise of the article is for someone who has the funding to replace/rebuild a computer, yet refuses to do so. Having upgraded the computer’s hardware and software – as you point out, resolves the issues related to outdated hardware and software. At which point only the chassis, the motherboard, and monitor remain obsolete.
Great suggestion for someone who will have the technical acumen to upgrade their computer internals.
Cheers!